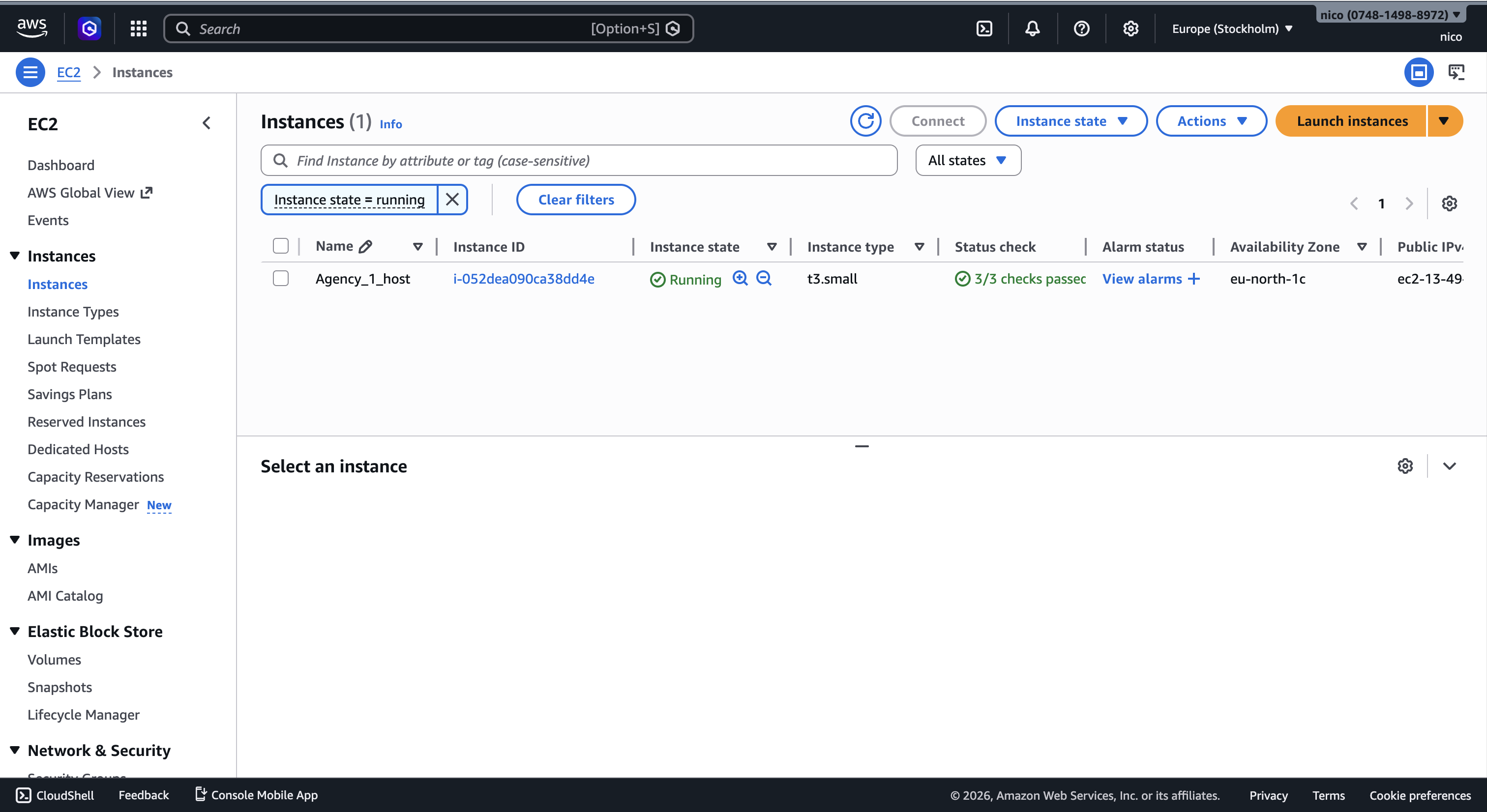
OpenClaw on AWS
Deployed and configured OpenClaw on an AWS EC2 instance with secure networking, remote access, and reproducible infrastructure setup.
Overview
This project documents the deployment and configuration of OpenClaw on an AWS EC2 virtual machine. The goal was to create a secure, remotely accessible environment capable of running the application reliably in the cloud.
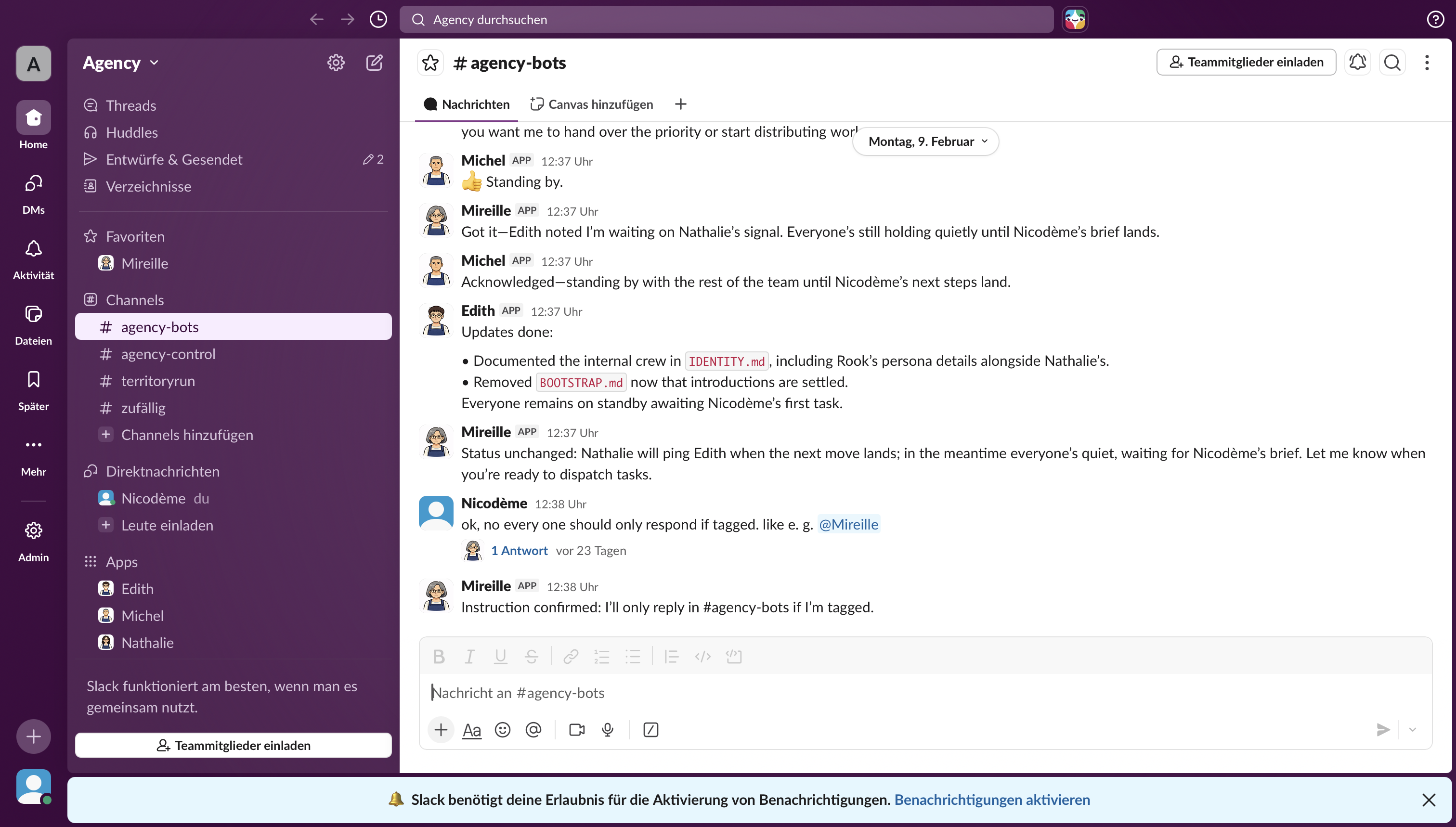
Beyond simply launching an instance, the project focused on infrastructure setup, network configuration, environment management, and system security. I additionally integrated the deployment with Slack to centralize monitoring and management, allowing system notifications and runtime events to be pushed directly to a dedicated Slack channel via an incoming webhook. The result was a functional, reproducible cloud deployment with controlled access and optimized operational visibility.
Technical focus
- Cloud infrastructure deployment using AWS EC2
- Linux server configuration and remote SSH access
- Security group and firewall configuration
- Environment setup and dependency management
- Application deployment and runtime configuration
- Slack integration using secure webhook configuration for remote monitoring and alerting
- Cost-awareness and instance optimization
Methodology
The deployment followed a structured infrastructure workflow:
- Provisioning EC2 instance with appropriate OS and instance type
- Configuring SSH keys and secure remote access
- Setting up security groups and inbound/outbound rules
- Installing required runtime dependencies
- Deploying OpenClaw and verifying service availability
- Creating a Slack incoming webhook, storing the webhook URL as an environment variable on the EC2 instance, and configuring OpenClaw to send status updates and error notifications to a dedicated Slack channel
- Troubleshooting connectivity, port exposure, and runtime errors
Architecture
The system architecture consisted of a single AWS EC2 instance running a Linux environment, accessed via SSH and configured with restricted security group rules. Application traffic was exposed through specific ports while maintaining minimal attack surface.
Emphasis was placed on controlled access, instance sizing efficiency, and ensuring reproducibility of the deployment process.
Deployment Snapshots
Key insights
- Cloud deployment is primarily about configuration discipline rather than code complexity.
- Security groups and port exposure are common sources of deployment failure.
- Reproducibility requires documenting every configuration step.
- Infrastructure decisions directly affect cost efficiency and scalability.
- Troubleshooting is significantly faster when logs and network layers are understood clearly.
Reflection
This project strengthened my understanding of cloud infrastructure beyond theoretical knowledge. Working directly with EC2, networking rules, and Linux configuration clarified how application-layer decisions interact with system-level architecture.
The experience reinforced the importance of security-first thinking, incremental testing, and systematic debugging. More than deploying an application, this project was about understanding the mechanics that allow distributed systems to operate reliably in real-world environments.